What are Stressers and DDoS-for-hire Tools?
Discover the role of stressers in modern network resilience testing.
Understanding Stresser Services
Online services designed to test the resilience of servers under
load called Stresser. They are specifically used to simulate Distributed Denial of Service attacks to check the protection of websites and servers. However,
some users exploit stressers to launch unauthorized Distributed Denial of Service attacks on sites
and applications, which is considered unlawful.
The ip stressers market involves renting out such services, allowing users
to initiate attacks on selected targets. This type of service often attracts attention due to its controversial nature,
and it is essential to understand all legal aspects and potential risks.
IP Spoofing and Layer 4 Attacks
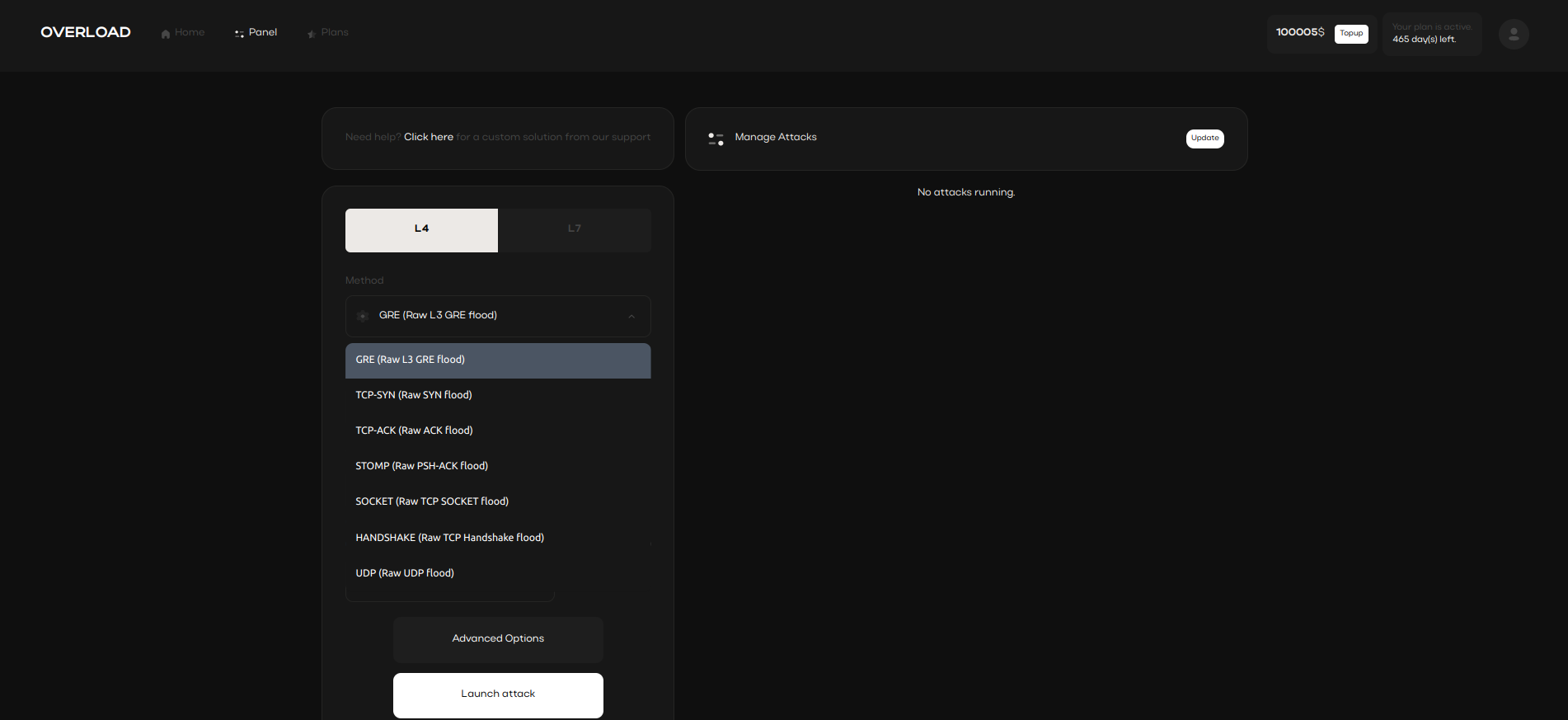
Network Layer 4 (L4) attack methods, commonly utilized in IP stressers, chosen specific network protocols to overwhelm servers.
One popular technique is address spoofing, where the attacker’s real IP address is hidden, making it difficult to trace.
These L4 methods and address spoofing tactics are frequently applied to bypass basic network security protections
and effectively simulate high traffic loads on a chosen server.
Booters and Their Uses

In addition to stressers, there are also booters
which serve a similar purpose. Booters are often used to simulate high traffic loads and identify weaknesses in systems.
These Distributed Denial of Service applications allow for a exclusive understanding of server durability. However,
misuse of booter services can lead to lawful issues due to unauthorized network attacks.
DNS/NTP/CLDAP Amplification Attacks

IP masking attacks can be enhanced through various reflection-based techniques, such as NTP, DNS, CLDAP increase.
These methods allow attackers to send small queries and receive significantly larger replies, amplifying the attack’s impact.
By using IP masking tactics, the attack origin is masked, making it challenging to trace
and prevent the traffic from overwhelming the target’s system.
- DNS reflection method
- NTP amplification
- CLDAP amplification
